Symmetric Vs Asymmetric Algorithms Computer Science Essay.
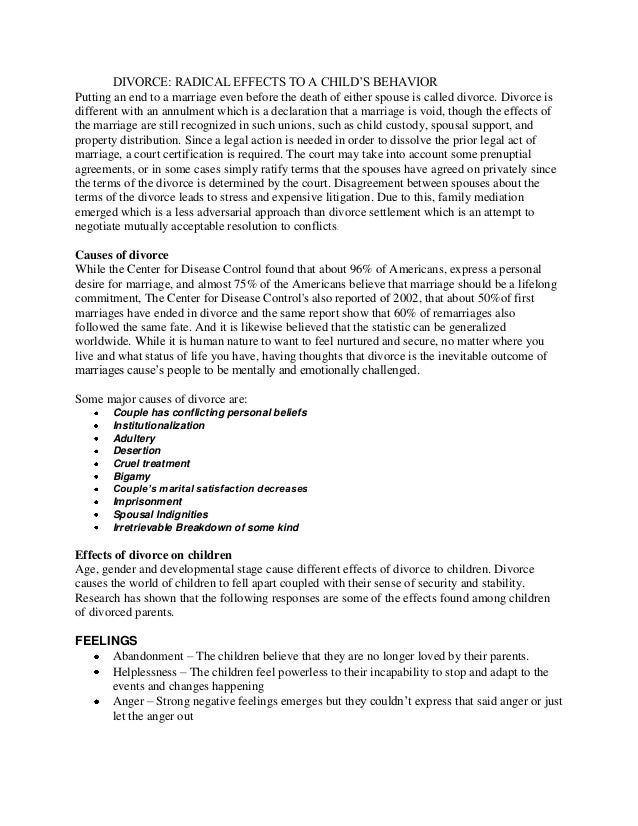
Difference between Symmetric and Asymmetric encryption. Symmetric: Asymmetric: Uses One key for encryption and decryption. Uses two keys, one for encryption and the other for decryption. Encrypted data and keys are exchanged. Only the encrypted data is exchanged and the public key is available for anyone. Quicker: Slow: Unmanageable if no of the participants become higher. Operations can be.
There is symmetric encryption and asymmetric encryption. It is the intention of this paper to describe both methods and give an opinion on which method to use to secure the sensitive date. When a symmetric encrypted key is used, both parties share the same key to both encrypt and decrypt data. Since symmetric encryption's use-case is to share information between users, each has to posses a.
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both encryption of plaintext and decryption of ciphertext.The keys may be identical or there may be a simple transformation to go between the two keys. The keys, in practice, represent a shared secret between two or more parties that can be used to maintain a private information link.
Asymmetric encryption was created to solve the problem brought about by Symmetric encryption. Let’s look at this illustration. User 1 has a sensitive document that he wants to share with User 2. He uses an encryption program to protect his document with a password that he chooses, and then sends the encrypted document to User 2. However, User 2 cannot open the message because he doesn’t.
Symmetric encryption is an old practice, while asymmetric encryption is relatively new. Asymmetric encryption was brought in to fix the problem of the necessity of sharing the key in the symmetric encryption model, removing the need to share the key by using in its stead a pair of public-private keys. Asymmetric encryption eats up more time.
Comparison Of RC5 And RC6 Block. Due to rapid growth in Internet and networks applications so the needs to protect such applications are increased. Encryption algorithms play a main role in information security systems. So it is desirable to develop a systematic understanding of database security concerns and their solutions and to come up with a framework. Ideally, such a framework should.
There are basically two types of cryptography technique- Symmetric and Asymmetric. Symmetric key algorithm is also categorized into two parts Stream Cipher and Block Cipher. In this paper, we analyzed feasibility of Symmetric Key Block Cipher Encryption techniques for storage space with their advantages and disadvantages and also presented the possible attacks on these algorithms. The main.